Cryptographic Privacy Meets Biosecurity: The Technical Architecture Behind Responsible DNA Screening
Cryptographic Privacy Meets Biosecurity: The Technical Architecture Behind Responsible DNA Screening
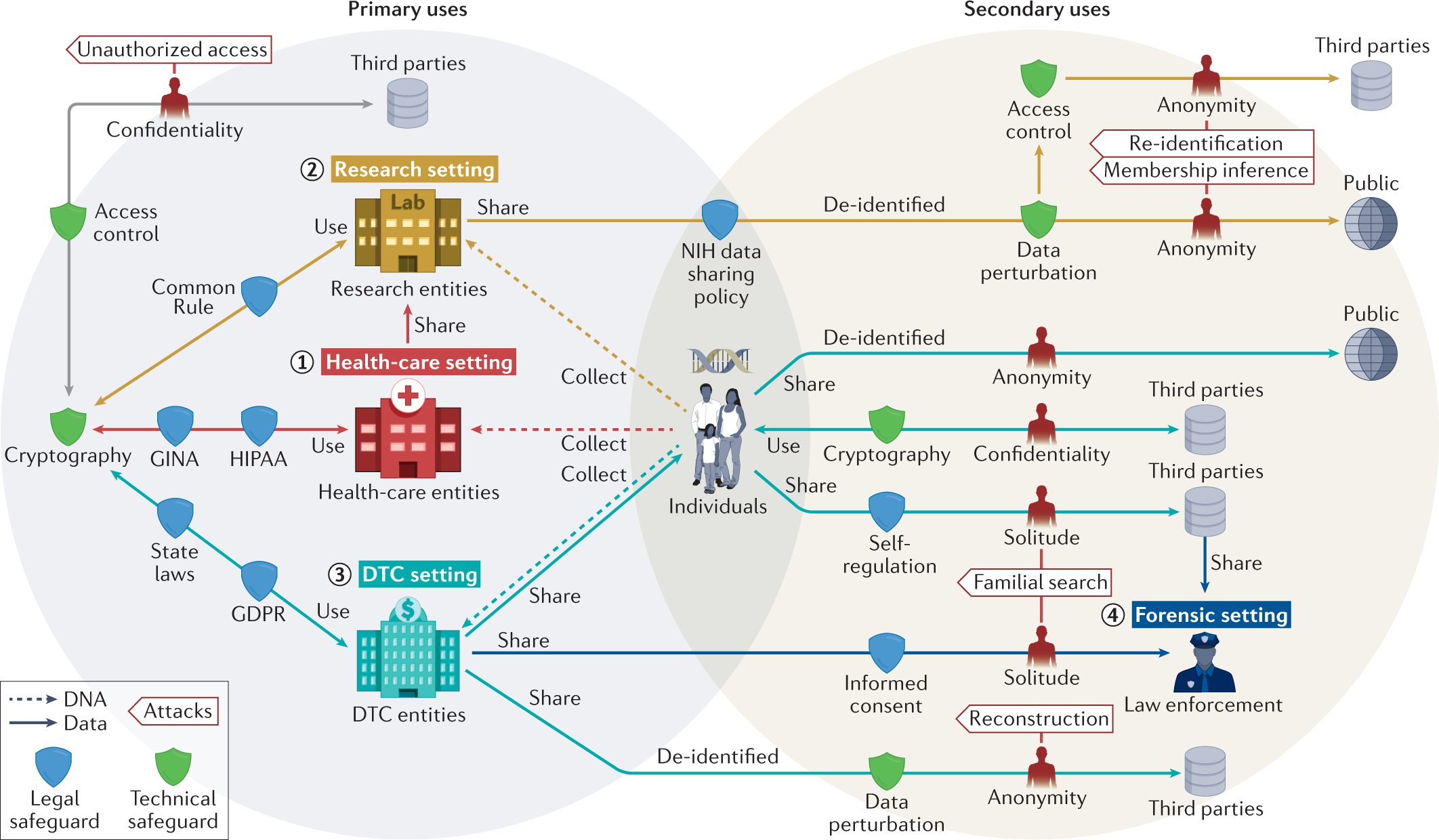
There is a fundamental tension at the heart of DNA synthesis screening that has slowed its adoption since the International Gene Synthesis Consortium first proposed voluntary screening guidelines in 2009. On one side sits the biosecurity imperative: every DNA sequence submitted for synthesis should be checked against a database of hazardous agents before it is manufactured. On the other side sits a legitimate scientific concern: submitting proprietary gene sequences to a third-party screening service means exposing intellectual property, unpublished research data, and potentially patentable genetic constructs to an external party.
For years, this tension was resolved — unsatisfactorily — by one of two approaches. Either researchers submitted sequences to screening services and accepted the privacy risk, or they avoided screening altogether and accepted the biosecurity risk. BioScreens, powered by the SafeDNA API, offers a third path: cryptographic screening that resolves the tension entirely, allowing sequences to be checked against a comprehensive hazard database without the raw sequence ever leaving the researcher's environment.
The Cryptographic Protocol
The technical approach underlying BioScreens DNA Sequence Screening is conceptually elegant. Rather than transmitting the raw nucleotide sequence to the screening server, the client-side application transforms the sequence using a cryptographic hash function — a one-way mathematical transformation that produces a fixed-length fingerprint of the input data. This fingerprint, called a hash, has two critical properties: it is computationally infeasible to reverse-engineer the original sequence from the hash, and any two sequences that differ by even a single nucleotide will produce completely different hashes.
The SafeDNA hazard database stores pre-computed hashes of known hazardous sequences — the genomic signatures of select agents, toxins, and potential pandemic pathogens. When a researcher submits a sequence for screening, the platform computes the hash of the submitted sequence and compares it against the database of hazardous hashes. A match indicates a potential hazard; no match produces a Granted decision. At no point does the raw sequence leave the researcher's environment, and at no point does the platform operator have access to the sequence content.
This approach is analogous to the way modern password authentication works. When you set a password, the system stores a hash of your password rather than the password itself. When you log in, the system hashes your input and compares it to the stored hash — confirming your identity without ever storing or transmitting your actual password. BioScreens applies the same principle to genomic data, with the additional complexity of handling variable-length biological sequences and managing the k-mer decomposition required to detect partial matches within longer sequences.
Beyond Simple Hashing: K-mer Analysis and Partial Match Detection
The naive application of cryptographic hashing to DNA sequences has an obvious limitation: a hazardous sequence embedded within a larger construct will not produce a hash match against the full hazardous sequence, because the hashes of the two sequences will be completely different. A researcher synthesising a 10,000 base pair plasmid that contains a 500 base pair region homologous to a select agent toxin gene would not trigger a match if the system only hashes the full submitted sequence.
BioScreens addresses this through k-mer decomposition — a technique borrowed from computational genomics in which a sequence is broken into all possible subsequences of length k (typically 30–50 nucleotides for biosecurity applications). Each k-mer is hashed independently and checked against the hazard database. This approach allows the platform to detect hazardous subsequences embedded within larger constructs, to identify partial matches that may indicate attempts to evade screening through sequence fragmentation, and to generate nucleotide-level hit region maps that show precisely where within the submitted sequence the hazardous elements are located.
The result is the interactive visualisation that BioScreens presents alongside each screening decision: a hit region map showing the full submitted sequence with hazardous regions highlighted, organism identification with accession numbers, and nucleotide-level annotations that allow a biosafety officer to understand exactly what was detected and why.
The Audit Infrastructure
Biosecurity screening is only as valuable as the audit trail it generates. A screening decision that cannot be documented, verified, or retrieved is of limited value to an institutional biosafety committee, a funding agency, or a regulatory body. BioScreens provides a complete audit infrastructure: every screening request is logged with a timestamp, the submitted sequence hash, the screening decision, and the full hazard breakdown. The history is filterable and searchable, and individual results can be shared via time-limited secure links — allowing a researcher to send a screening result to a collaborator or an IRB reviewer without requiring them to create an account.
The PDF report generated by BioScreens is formatted for direct submission to institutional compliance systems, with the screening decision, hazard breakdown, and platform metadata presented in a standardised format that biosafety committees can evaluate without requiring technical expertise in genomics or cryptography.
Implications for the Synthetic Biology Ecosystem
The biosecurity challenge posed by synthetic biology is not static. As sequencing costs fall and AI-driven protein design tools like RFdiffusion and ProteinMPNN make it possible to design novel proteins with specified functions from first principles, the set of sequences that require biosecurity evaluation is expanding beyond the known hazard database. A sequence that has never existed in nature — designed by an AI to fold into a structure with toxin-like properties — will not match any entry in a database of known hazardous sequences.
This is the frontier challenge for DNA synthesis screening, and it is one that cryptographic hashing alone cannot address. BioScreens' integration of AI-powered DURC analysis alongside its sequence screening tool represents an acknowledgment of this limitation: sequence-level screening catches known hazards, while document-level AI analysis catches the research context that might indicate novel hazard creation. Together, the two tools provide a more comprehensive biosecurity posture than either can achieve alone.
For the synthetic biology community — and for the biosecurity professionals, IRB members, and policy makers who are responsible for governing it — BioScreens represents a meaningful advance in the infrastructure available for responsible science. The tension between scientific privacy and biosecurity compliance, long treated as irreconcilable, turns out to be solvable with the right cryptographic architecture.
Reference: BioScreens Biosecurity Intelligence Platform — https://www.bioscreens.org/